Security governance, risk and compliance (GRC) should be a strategic enabler for technology companies. In practice, many organizations experience the opposite: fragmented processes, blurred accountability and growing compliance obligations that feel disconnected from how the business actually operates.
For chief information security officers (CISOs) in the technology sector, the challenge is not a lack of effort or intent. It’s that security GRC in tech is fundamentally harder to do well.
Rapid innovation cycles, complex product ecosystems, frequent acquisitions and evolving regulatory expectations create an environment where traditional GRC models often struggle to keep pace. As a result, security leaders are left trying to balance risk management, compliance and business enablement — often with limited visibility across the full risk landscape.
The good news is that effective security GRC is achievable. Based on what we see across leading organizations, success comes down to a few foundational decisions and disciplines.
Below are five practical tips to help CISOs and security leaders build a security GRC program that scales with the business and delivers meaningful insight — not just compliance artifacts.
1. Start With Strategy, Not Structure
One of the most common missteps in security GRC is starting with organizational structure or tooling before clearly defining strategy.
A successful GRC program looks very different depending on the organization. A high-growth technology company seeking to increase its marketability through additional certifications will make different trade-offs than a mature enterprise focused on driving risk-based decision-making. Neither approach is inherently right or wrong — but misalignment between strategy and execution creates friction quickly.
Security leaders should start by answering a few core questions:
- Is the organization primarily risk-centric, compliance-driven or somewhere in between?
- What is the enterprise’s tolerance for risk, particularly as it impacts decisions made by the business or in relation to emerging technologies?
- How do technical debt and immature processes affect control effectiveness and scalability?
Without clarity on these points, security GRC teams often find themselves reacting to issues rather than guiding decisions. Strategy provides the lens through which priorities are set, investments are made and success is measured.
2. Clearly Define Ownership and Accountability
Security GRC does not operate in isolation. It intersects constantly with first-line business teams, other second-line risk functions and third-line assurance groups.
High-performing organizations intentionally design for aligned assurance, reducing duplication while improving insight. Instead of multiple teams collecting similar data for different purposes, information flows across domains in a coordinated way. Without this intentional design, fragmentation can lead to gaps in accountability, particularly when issues arise: Who owns remediation? Who has the authority to enforce compliance? And who is accountable when risk decisions are made — or deferred?
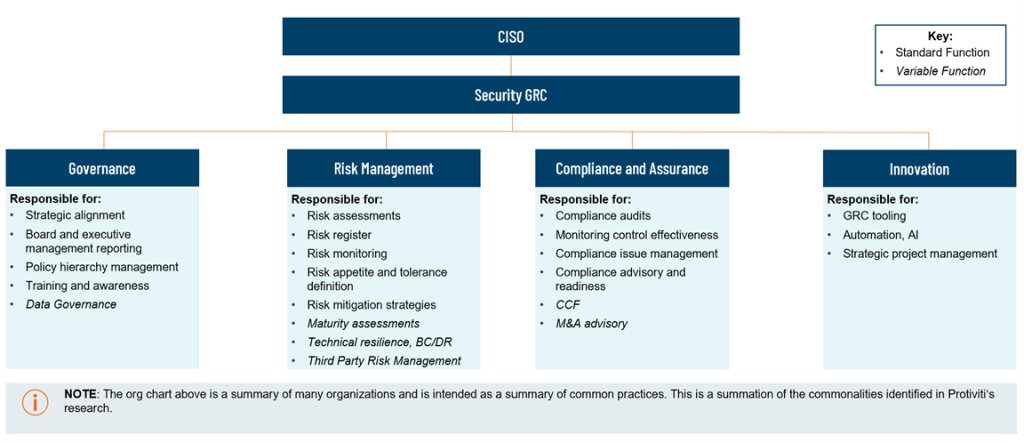
When evaluating how GRC best fits into this greater organizational matrix, many clients have asked what other GRC functions are responsible for. According to recent Protiviti benchmarking, there is no constant model for what GRC owns across all companies. However, common patterns emerge in what GRC typically oversees. A model has been shared below to represent that most common structure and responsibilities of GRC functions at technology companies we work with, as well as to identify some of the components of GRC that are variable (responsibilities that may or may not be assigned to GRC).
An innovation function is a relatively new domain under the GRC umbrella; it serves as the tooling and automation hub with dedicated engineering resources to drive continuous improvement and strategic initiatives like continuous monitoring.
To complement the responsibilities shown above, clear ownership and well-defined touchpoints with other assurance functions are critical to guarantee an effective program.
Just as important, leaders ensure that ownership comes with authority. Security GRC teams must be empowered to hold stakeholders accountable, escalate issues when needed and influence outcomes — not just document findings.
3. Create Cross-Functional Processes That Build on Each Other
In many tech GRC organizations, responsibilities across GRC functions are fragmented or overlapping. Risk teams assess threats, compliance teams test controls and governance teams manage policies — often in parallel, but not always in coordination. Leading-practice GRC functions create clear channels of communication between their domains to ensure sharing of knowledge and, more importantly, shared data to build from.
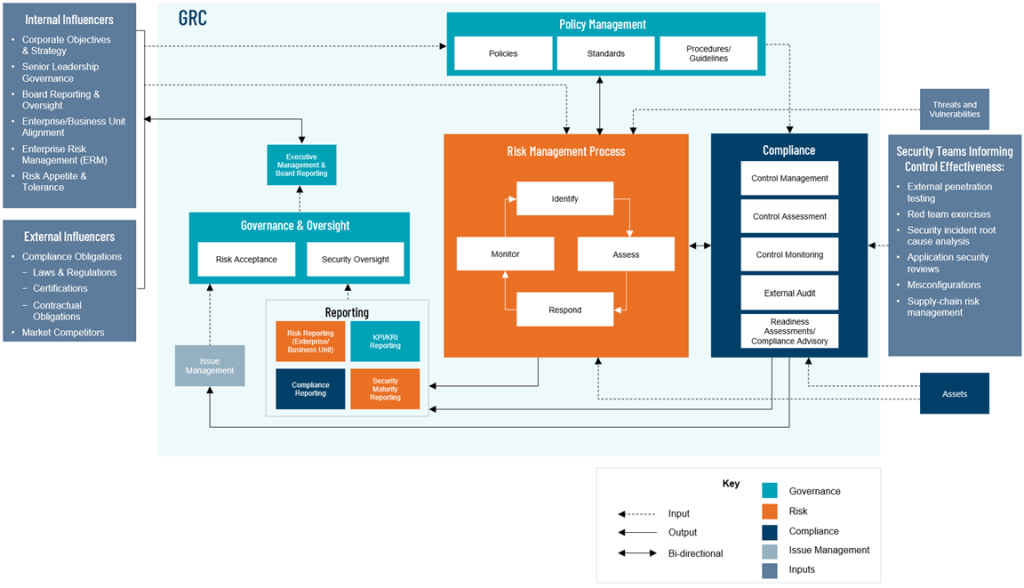
The image below shows that in leading-practice GRC functions, there are continuous, evolving connections between the governance, risk and compliance domains, including, for example, the following:
- Compliance findings often highlight systemic issues that should inform risk assessments.
- Risk teams may identify emerging threats that require updates to policies or standards.
- Governance decisions should reflect both operational realities and required compliance outcomes.
When data is shared effectively (often supported by GRC tooling), leaders gain a more holistic view of risk. This single, integrated perspective enables better decision-making and more meaningful conversations with executives and boards.
4. Measure Maturity and Design for Scale
Another common challenge is growth. As organizations expand, security GRC scope increases, but processes do not always scale at the same pace. The result is an overreliance on manual effort and incremental headcount, which becomes unsustainable over time.
Leading organizations regularly assess the maturity of their core GRC functions across governance, risk and compliance. These assessments highlight where processes are well-defined and scalable, and where gaps exist.
Key questions include the following:
- Are processes documented and repeatable, or do we rely on individuals with internal know-how to get things done?
- Do processes scale with business growth, or do they require increasing headcount time after time?
- Are there maturity imbalances across domains that create bottlenecks?
- What is the right level of maturity for our organization to ensure that we meet the vision or strategy we’ve set for ourselves?
By understanding current-state maturity, security leaders can prioritize investments and avoid spreading resources too thin. This disciplined approach also sets the foundation for future automation.
5. Prepare for Automation and AI — but Get the Basics Right First
There is growing interest in using automation and artificial intelligence to improve security GRC efficiency and insight. While these technologies offer real potential, however, they are dependent on sound processes and quality data.
Automation amplifies what already exists. If underlying processes are inconsistent or data is unreliable, tooling will simply accelerate the problem.
Organizations that succeed with GRC automation focus first on:
- Standardizing core processes
- Improving data quality and consistency
- Defining clear inputs, outputs and decision points
Once these fundamentals are in place, technology can enable faster risk identification, more timely reporting and better visibility across the enterprise. Given how quickly GRC platforms are evolving, organizations that delay this groundwork risk falling behind.
Moving Forward
Security GRC in tech will always be complex — but it does not have to be reactive or burdensome. By grounding the program in strategy, clarifying ownership, aligning across functions, measuring maturity and preparing thoughtfully for automation, security leaders can transform GRC into a true business enabler.
How Protiviti Can Help
Protiviti helps organizations across every stage of their security governance, risk and compliance (GRC) journey. With deep expertise and industry depth, Protiviti delivers tailored solutions to meet clients’ needs. To hear real-world success stories and practical lessons on scaling security GRC from leading tech organizations, join us on April 16 for our webinar “Navigating Tech’s Toughest GRC Challenges: Lessons in Efficiency, Innovation and Automation.”